4 Requirements of Self-hosting and their Key Uses.
Self-hosting is the alternative technique of hosting your websites with the help of third-party vendors or Cloud storage solutions. People these days are considering self-hosting privacy techniques for their preferred security features. The Internet these days is centralized. They depend on a single location from which we access custom RSS feeds. This may cause users
Self-hosting is the alternative technique of hosting your websites with the help of third-party vendors or Cloud storage solutions. People these days are considering self-hosting privacy techniques for their preferred security features. The Internet these days is centralized. They depend on a single location from which we access custom RSS feeds. This may cause users to depend on the centralized network for web access.
TechJury says that 67% of the enterprise runs their business in cloud infrastructure. Though these technologies come with multiple security features, there may be cases when users have to depend on the host for accessing the data. Keep reading this article to explore the benefits of self-hosting.
Table of Contents
- Centralized Hosting
- Problems with Centralized Hosting
- What Is Self Hosting
- Self Hosted Privacy
- Requirements for Self Hosting
- Centralized Hosting vs. Self-Hosting Services
- Why Choose Proxyscrape for Self-Hosting?
- Frequently Asked Questions
- Conclusion
Centralized Hosting
Working of Centralized Hosting
In centralized hosting, members depend on the common server to run their applications and perform operations like accessing, storing, and processing. The Internet is becoming a huge centralized hosting system, where people rely on common servers to access their custom RSS feeds.
Consider using Gmail, Google Docs, Google Drive, or Google Sheets. As these web applications are running on a Google server, people have to access the Google web Interface to avail of their web services. Here, the Google server is the centralized host of their web services. Popular websites or web interfaces act as a centralization medium.
Among the social sites. Facebook acts as the centralized web server, whereas a few other social web services directly use the Facebook data of the user to log in to their sites. The centralized web server passes the data to their dependent sites by using an extremely lightweight data format, JSON. Go through our blog to learn more about how to read and parse JSON using Python.
Problems with Centralized Hosting
Amazon Web Services and other cloud storage platforms offer centralized hosting services for most of the network activities. This centralization is the most recent and common technique with multiple benefits and drawbacks altogether. Though this method ensures proper security measures and reduces the physical storage area, they come with an equal number of drawbacks too. Some of these drawbacks are
Popular Companies that Dominate the Field
A few established companies, like Facebook, Google, and YouTube, with their popularity, attract all kinds of users on the internet. These companies tend to collect and store user data in them and this causes other companies to rely on these servers for information. This centralization makes developing companies pay the popular ones to use their storage database.
Security Threats and Privacy Issues
Standard centralization and cloud storage provide quality cyber security measures. Still, when people host their sites and run their businesses online, there are high chances of security attacks. Cyber attackers may hack organizational information or personal user data, as well as the transaction database through harmful phishing emails. The centralized servers may get exposed to security threats when the hosting media gets wider with a huge set of data and new clients.
A Single Point of Failure
A Single Point of Failure is an outage caused at one point in the system. As most web services and web applications are dependent on a few servers, a simple outage in the main setup of the server may affect the service of all of them at the same time. Facebook suffered an outage for over 6 to 7 hours in the year 2021. During this time Facebook along with its subsidiary applications stopped functioning.
What Is Self Hosting
Working of Self-hosting
Self-hosting is the process of hosting your websites from your own server. You can install a server of your own and handle the web services, smart devices, and web applications by yourself, without depending on a third party. Self-hosting method requires a dynamic DNS service and network connectivity from Internet Service Providers. Apart from that, you don’t need to depend on other vendors to access and handle your database and services. Home network requirements and small-scale businesses can choose self-hosting for a highly secured environment.
Self Hosted Privacy
One of the best features of a Self-hosting service is self-hosted privacy. When users depend more on other parties, the data may lack privacy. Some services providers also take control of data so people can not access it whenever they want. This may also bring down the security of the data. Giving others control of the data is not a safe practice. In this case, self-hosting websites from your own server can ensure 100% data control and reduce the risks of cyber attacks as you have complete control over the system.
There are enough self-hosted privacy tools in the market that automates the self-hosted system and runs the websites. Improving the security features of this method depends on proxies to prevent the data from cyber-attacks. Proxy vendors, like ProxyScrape, furnish quality dedicated proxies with many features at a reasonable rate that can suit a self-hosted system.
Requirements for Self Hosting
To set up a self-hosted environment, you will require a set of components like
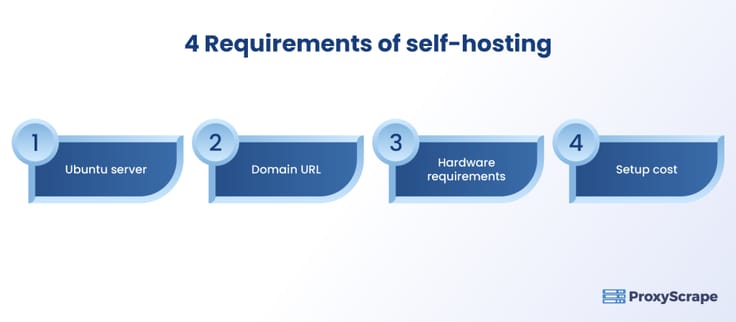
4 Requirements of Self Hosting
A Server
You will require a server of your own to support the functionalities of the client. Your websites, web applications, and other services will access data from your web server so you can have complete control over the functionality and database. Ubuntu server is suitable to host your own services.
Example: WhatsApp and Instagram are dependent on Facebook’s server. Unlike them, you can host your web app from your server.
A Domain URL
Every page on the internet has a Universal Resource Locator (URL) to uniquely identify a page. Among the URL components, the ‘domain component’ is the one that comes after ‘@’ and denotes the main server or identity of the web page.
Example:
“[email protected].” Here the address has the domain name of the centralized web host “Yahoo.”
Instead of using this, you can use your domain with your company name as a domain.
Example: ProxyScrape.com
Here, the company has secured its domain with the name “PROXYSCRAPE.”
Installation Requirements
To set up a server, you have to buy physical hardware and undergo the installation process. Also, make sure the server is compatible with all the software and the applications you require in your business. You can also use a virtual server as utilizing a virtual server on your own can help you with self-hosted alternatives. Self-hosting services are compatible with all Operating Systems, like Linux, Ubuntu, and Windows. People can use the Ubuntu desktop as an Ubuntu server to self-hos their site.
Installation Setup Cost
Making sure the setup costs fall under your budget is the most significant thing on the checklist. Considering the needs of the business and choosing suitable methods and components can help you save money.
Centralized Hosting vs. Self-Hosting Services
| Centralized Hosting | Self-Hosting |
|---|---|
| Uses a cloud or common network to host the web services. | Uses its own setup to host web applications and services. |
| Should depend on the main host for data and control. | Has complete control over the data and operations of the website. |
| Possibilities of cyber threats. | Data here are highly secured, as they do not involve other parties in their system. |
| Users can switch to self-hosting services at any time. | Switching to centralized hosting requires some installation. |
| Suitable for all sorts of businesses. | Suitable for small-scale businesses and home network applications. |
| Best suited for large-scale businesses. | Best suited for companies who want to create a self-sufficient workplace and network. |
Why Choose Proxyscrape for Self-Hosting?
High Bandwidth – Proxyscrape provides proxies with unlimited bandwidth, making it easy for self-hosting methods to handle high-dimensional multimedia data on their own.
Uptime – Proxyscrape ensures 100% uptime. Proxies function throughout the day so that self-hosts can keep functioning all the time.
Multiple Types – A good proxy provider should furnish a proxy of all types to fulfill the user’s requirements. Proxyscrape provides shared proxies, like datacenter proxies, residential proxies, and dedicated proxies, like private proxies.
Global Proxy – We offer proxies from more than 120 countries. There are also proxies for different protocols, like HTTP proxies and Socks proxies.
Cost-Efficient – Here, the premium proxies are of reasonable costs and have high bandwidth. Check out our attractive prices and huge proxy options.
Proxyscrape is the proxy provider solution that uses proxies for multiple applications. One among them is proxy sites or proxy servers that bypass the restrictions across geographical locations. The anonymity and the scraping features of the Proxyscrape proxies allow the users to unblock the restricted content. Dedicated proxies will have a unique IP address for each user so that the web servers and ISPs will not easily track the identity of the users. Shared proxies like datacenter proxies and residential proxies provide proxy pools with different proxy types to unblock the blocked sites with multiple proxies.
Frequently Asked Questions
FAQs:
1. Which proxies can help self-hosted privacy?
2. Is the self-hosted privacy method free from system crashes or failures?
3. What is the difference between self-hosting and centralized hosting?
Conclusion
There is a myth among people, who believe self-hosting alternatives are traditional and outdated methods. People rarely understand that the self-hosting method removes the dependency and allows you to develop an independent solution on your own. If your business scale is large and requires integrating with a popular web service, choose cloud or other companies to support your business. If your solution is small and you focus more on having full access to data with high security, make use of the self-hosted privacy system.