What is a Reverse Proxy? 4 Key Uses

Reverse Proxies work on behalf of web servers and ensures their anonymity. According to a web tech survey, nearly 33% of websites use reverse proxies. Usually, people speak about proxies that work on behalf of the client to hide the identity of the client from web servers. But, have you ever thought of the other
Reverse Proxies work on behalf of web servers and ensures their anonymity. According to a web tech survey, nearly 33% of websites use reverse proxies. Usually, people speak about proxies that work on behalf of the client to hide the identity of the client from web servers. But, have you ever thought of the other types of proxies that can act on behalf of the server? Can people use proxies to secure the servers’ identity? This article will address this functionality of proxies and elaborate on how the reverse proxy works and how they are different from the usual one.
Table of Contents
- What Is a Reverse Proxy?
- General Purpose of Proxy Servers
- What Is a Forward Proxy?
- What Is a Reverse Proxy?
- Reverse Proxy and Forward Proxy
- Types of Reverse Proxies
- Why Do We Need Reverse Proxy?
- Forward Proxy vs. Reverse Proxy
- Frequently Asked Questions
- Summary
What Is a Reverse Proxy?
A reverse proxy acts as a representative of the server end to keep their identity from the network with the proxy addresses. This proxy type receives incoming requests from the client side and responds to them back on behalf of the server.
General Purpose of Proxy Servers
Proxy servers usually assists applications with simplifying and automating the process of scraping data. Data extraction becomes easier with proxies, as they provide access to all sorts of locations and operate at high speed. Proxies act as intermediary devices between the nodes in the network and can route the information to the destination by hiding the identity of the devices.
What Is a Forward Proxy?
Before discussing the reverse proxy, having a brief discussion about the forward proxies can make it easier to understand reverse proxies better. The term proxy generally refers to forwarding proxies that are more commonly used. Forward proxies are proxies that sit between a client and a server in the network and work on behalf of the client. The forward proxy forwards client requests to the network with their proxy address. By this, other nodes or web servers in the network are not aware of the actual IP address of the client and consider the proxy server’s address the real client’s address location. This technique allows the client to scrape a large amount of data from the network by using multiple IP addresses of the proxy. They can also increase the web traffic using this forward proxy by utilizing multiple IP addresses to fake real human traffic.
What Is a Reverse Proxy?
Working of Reverse Proxy
Reverse proxies work to ensure protection to the server side of the communication. Reverse proxy services act as an internal server, where the proxy works on behalf of the backend servers. A reverse proxy sits in front of the web servers to keep the identity of the servers under wraps. Reverse proxies receive incoming requests from clients and return them with a response from web servers. The clients will only know the intermediate reverse proxy they are communicating with. This helps web servers to stay anonymous from public internet users and can prevent overcrowding of the official web servers.
Reverse Proxy and Forward Proxy
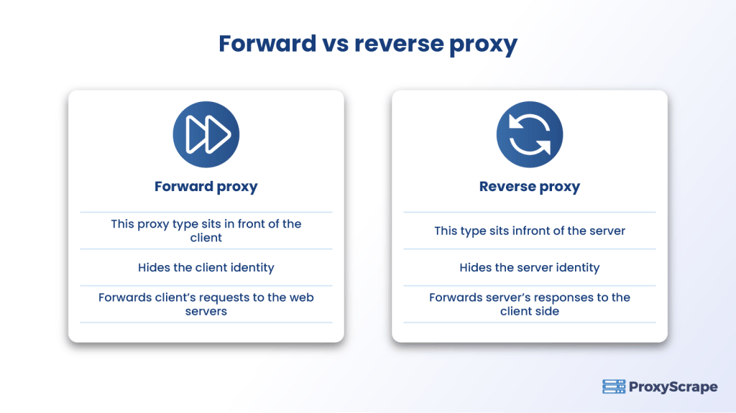
Both forward and reverse proxies have the basic qualities of proxies. Their primary focus is to hide the IP address of the device they work for and ease the process of surfing and scraping on web pages. Though both proxies act as a bridge between network nodes and forward requests, or responses representing the other nodes, they vary on certain factors, like for whom they work and where they are located in the proxy network.
Forward proxy servers concentrate on protecting the client’s side while basic reverse proxy servers protect the backend server. The proxy server forwards requests from the client to the internet network with their proxy address. So, other servers will not know the source location of the request. This helps clients avoid IP blockades. They can scrape information at high speeds across any geographical location. Reverse proxy servers receive requests from the client as internal servers and route the response from the server to the client. By this, the reverse proxy protects the identity of the server. For example, some popular business institutions will have many clients or visitors on their websites. To control overcrowding in their website’s origin server, they use reverse proxies as their representative to pass the information people request without letting the people directly access their sites.
Types of Reverse Proxies
The reverse proxy has two types according to their functionalities and usage. Though all the reverse proxies are similar in the working model, they may vary with some unique features to distinguish themselves from the basic reverse proxy.
Basic Reverse Proxy
The regular reverse proxies are used for security purposes, like maintaining a secured environment of the web servers by using the reverse proxy to communicate with people rather than exposing their true IP addresses. These reverse proxies receive incoming requests from the clients, forward them to the servers, and return the response from the server back to the clients.
Load Balancing Reverse Proxy
Load balancers are also a type of reverse proxy and they represent the server-side, as well as handle multiple web servers. When the communication network has more than backend servers, load balancers will also take care of splitting tasks among the servers. This type is responsible for the even distribution of loads among the servers. This process optimizes resources and reduces processing time.
Why Do We Need Reverse Proxy?
Load Balancing
Popular websites with a huge market value in the field may have millions in traffic on their servers, and the popularity can keep on increasing day by day. Here comes a situation where websites cannot handle the huge mass of traffic with a single backend server and the page loads start to take time. They can eventually end up using multiple servers to handle the incoming traffic. Load balancing reverse proxies help the website handle one or more servers with a load balancer solution. This load balancing technique performs traffic routing by forwarding the incoming requests to another server when the initial one is overloaded. This makes use of the available back-end server at that moment to serve client requests.
Global Server Load Balancing
This global load balancer is more relevant to general load balancing servers in the case of distributing traffic among the servers. The difference is that the global server load balancer can distribute globally client requests among the servers. This benefit of using any server around the globe can help servers to use the nearest possible server to process incoming traffic and respond to them. This method decreases the distance and time for the clients and servers.
Encryption
In the client-server communication model, encryption takes a major role. The origin servers have to decrypt the requests from the client and send the responses in encrypted form. This may be a tedious process for the original server, which takes care of all the backend processes. To ease this encryption process, the reverse proxy can auto-encrypt and decrypt messages.
Distributed Denial of Services Protection
Reverse proxies are the most suitable processes to use to protect business people from Distributed Denial Of Services (DDOS) Attacks. This attack is a cybercrime in which the attackers target the web server and dump them with loads of requests. So, the web server crashes, finding it hard to withstand the bombarding web traffic. To handle these DDOS attacks, reverse proxies help by acting as an intermediary between the attackers and the server side. As all the web traffic goes through the proxy gateway, it only allows normal and organic traffic to get through them and prevents malicious traffic from reaching the server. Instead, they use the caching system to cache the response from the actual web server and send them to the clients through the reverse proxy server. This helps them to prevent suspicious emails or messages by using cryptography techniques.
Caching the Information
When intermediate servers forward incoming requests to the web server, collect the response from the web server, and deliver the response to the client. These internal servers also record the copy of the response as cache memory. Some frequent requests from clients will have the same responses and so reverse proxies can cache the response and reply to clients with a quick reply without reaching the origin server every time.
Forward Proxy vs. Reverse Proxy
Check out our article on “Forward Proxy vs. Reverse Proxy”
Forward Proxy vs. Reverse Proxy
| Forward Proxy | Reverse Proxy |
|---|---|
| Sits in front of the client | Sits in front of web servers |
| Hides the client’s identity | Hides the server’s identity |
| Forwards the client’s request to the server | Forwards the server’s response to the client |
| Helps the client access restricted web content by staying anonymous | Helps the server to avoid overcrowding in their sites and stay anonymous from clients |
Frequently Asked Questions
FAQs:
1. What is a reverse proxy?
2. What is the difference between forward proxies and reverse proxies?
3. What are the uses of reverse proxies?
Related Articles
How to Use Reverse Proxy to Install a WordPress Blog?
Summary
Reverse proxy servers highly concentrate on web application security from the server side. Business owners can make use of the reverse proxy to protect their sites from hackers and malicious attacks. As reverse proxies forbid the direct access of users with the primary server, it prevents unnecessary crowding on the site. Business marketers can provide users with needed information and still restrict them from accessing primary sites for security purposes. Proxyscrape proxies support reverse processes to protect servers from cyber attacks. These reliable proxies help users in unlimited scraping at high speed and are also cost-efficient. Buy the proxy of your desired location and type as they provide proxies of every location address to overcome geo-restrictions.